By Brian T. Horowitz, Editor and Contributing Writer
The RSA Conference in San Francisco, held April 20-24, brought stimulating discussion on topics such as threat intelligence, privacy and cloud security.
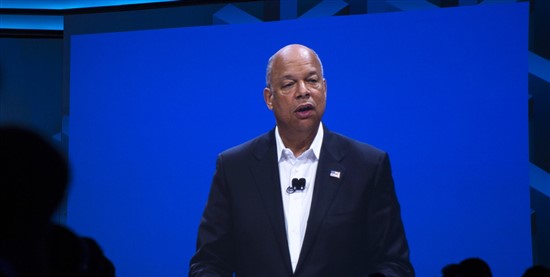
Featured keynotes included Homeland Security Secretary Jeh Johnson, Scott Charny, corporate vice president for Microsoft’s Trustworthy Computing Group, and Andrew McAfee, associate director of the Center for Digital Business at the MIT Sloan School of Management, who in his “Second Machine Age” talk described how devices from science fiction are becoming reality.
The first day of a packed week of events featured the “Most Innovative Company” competition on April 20, in which enterprise security application vendor Waratek took the honors. Waratek offers a runtime application self-protection solution for Java.
“Winning the Innovation Sandbox competition as the Most Innovative Company at the RSA Conference is the highest honor for a startup information security vendor,” said Brian Maccaba, Waratek’s CEO, in a statement. “Being selected by a panel of judges that represents a ‘Who’s Who’ of the security industry is a powerful endorsement for our technology, market opportunity and the value we provide customers.”
On the security beat
In a April 22 session called “Gumshoes Part Deux — Security Investigative Journalists Speak Out,” security journalists discussed the pitfalls as well as success stories in covering threats and data breaches.
One of the biggest challenges is figuring out which breaches to cover since they’re becoming too frequent.
“We can’t cover every breach anymore,” said Nicole Perlroth, an investigative reporter for The New York Times. “We don’t cover every murder in NYC.”
Perlroth told her story of hacking into the videoconferencing equipment of a leading investment-banking firm, telling the company about it and then writing up the story. “They said we don’t think this happened,” Perlroth said.
A key point raised throughout the conference was the need for more threat intelligence to help chief information security officers keep systems secure.
“Failure to share information in a timely way causes a lot of problems,” noted Brian Krebs, author of the blog Krebs on Security.
Perlroth agreed.
“It does seem like that’s one of the biggest missing links right now,” she said.
Check out our slideshow below to see highlights from the RSA Security conference in San Francisco.

RSA 2015 in San Francisco
RSA 2015 covered the key topics in IT security, including privacy, encryption, cryptography and threat intelligence.
Keynote speakers at RSA 2015
Keynote speakers at RSA included long-distance swimmer Diana Nyad, actor Alec Baldwin, presidential historian Doris Kearns Goodwin and Scott Charney, corporate vice president for Trustworthy Computing at Microsoft.

RSA 2015 “Most Innovative Company”: Waratek
At the RSA Conference's Innovation Sandbox, the "Most Innovative Company” honor went to Waratek, which offers a runtime application self-protection solution for Java. To solve the problem of Java apps not being able to test, diagnose or protect themselves from vulnerabilities, Waratek packs Java applications inside virtual containers.
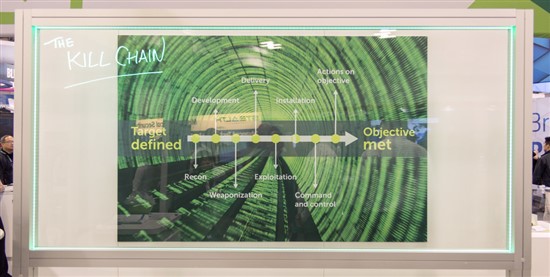
RSA 2015: Kill Chain illustration
Originated by Lockheed Martin and shown at the Dell booth at RSA, the Kill Chain is the process the threat actor goes through when targeting an organization. “If companies want to assess how their security is shaping up, they can map it to the kill chain,” said David Lorti, product marketing manager for SRC at Dell SecureWorks.
RSA 2015: SonicWall
Dell showcased its SonicWALL SuperMassive 9400, a firewall that performs deep-packet inspection and supports millions of simultaneous connections at near-zero latency.
RSA 2015: Intel Booth
At RSA, Intel discussed how to secure embedded devices and Chris Young, its senior vice president and general manager, suggested in a keynote that companies need to find a way to put intelligence about threats to better use.
RSA 2015: Dell Seminar
Dell’s Tim Brown, John McClurg and Jon Ramsey (right) joined moderator Wendy Nather of 451 Research for a lively discussion on security’s role as an enabler to the business.
RSA 2015: Social Media Lounge
The RSA conference had a constant feed of information, and attendees could easily stay connected to streaming keynotes and Twitter conversations.
RSA 2015: Homeland Security's Jeh Johnson
"Counterterrorism is the cornerstone of my department’s mission, but the reality is in 2015 cybersecurity has become a mission of equal importance," said Department of Homeland Security Secretary Jeh Johnson in a keynote address.
RSA 2015: Homeland Security
The Department of Homeland Security is looking to foster a stronger partnership with the private sector in fighting cyber crimes and also aims to work closer together with other agencies to share information on cyber threats.
RSA 2015: Security Journalism
Wired magazine's Kevin Poulsen, Brian Krebs of KrebsonSecurity, The New York Times’ Nicole Perlroth and Thomson Reuters' Joseph Menn (from left) discussed their challenges as journalists when covering data breaches. Dan Hubbard, chief technical officer at OpenDNS (far left), moderated the panel.